Cloud Security
Merchants, Do You Know Where Your Card Data Is?

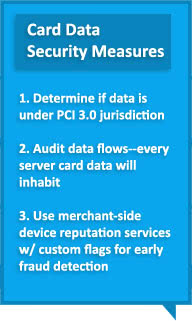
Card fraud affects merchants, not just shoppers. The Data Security Standard 3.0, released by the Payment Card Industry (PCI), urges companies to create a data flow diagram. This diagram would reveal all the systems, applications and employees who have access to cardholder data.
In the majority of compromises we’ve seen over the past few years, the merchant was trying to do the right thing but was unaware that cardholder data existed in a location that was not being protected,” states Troy Leach, PCI’s Security Standards Council chief technology officer, to StorefrontBacktalk.
Data flow diagrams include all types of data pertaining to users, suppliers and customers, and businesses should do a full analysis of their systems to know what’s what.
Businesses should also learn details about security levels at all stages, and figure out whether different data is covered under PCI jurisdiction or the protocols of foreign entities.
Data must be “overlaid with a diagram of servers on- and off-premise, and all mobile devices, including those owned by employees,” reports PaymentsSource.
Merchants should know where all their cardholder data is; how their organization operates; and “how their customer’s cardholder data moves throughout their environment,” says Leach, so they can formulate decisions that will minimize risks and costs.
 PaymentsSource recommends mapping the application of data flows, since businesses today are “super-interconnected” to other networks.
PaymentsSource recommends mapping the application of data flows, since businesses today are “super-interconnected” to other networks.
January of 2015 is when PCI’s Security Standard 3.0. will be in full effect. In the meantime, retailers should promptly start creating data flow diagrams.
Oregon-based iovation Inc. has created an exclusive network of global brands across the retail industry and others, with thousands of fraud professionals reporting more than 10,000 fraud and abuse attempts each day.
iovation’s shared database contains more than 1.6 billion unique devices including PCs, laptops, iPhones, iPads, Android, Blackberries—practically every Internet-enabled device that exists.
Many big brand retailers use this device reputation service to detect fraud early by not only customizing their own real-time rules to set off triggers, but by leveraging the experiences of other fraud analysts to know if the device touching them at this moment has been involved in chargebacks, identity theft, bust-outs, and any other kind of online abuse you could imagine.
[This post originally appeared on HackSurfer and is republished with permission.]
Learn more about cloud security and infrastructure monitoring software by downloading our free Top 10 IT Infrastructure Monitoring Software comparison report.






