How to Successfully Integrate Security into DevOps

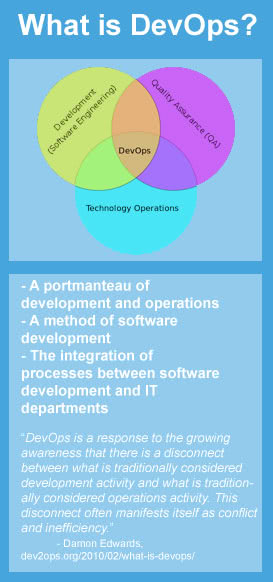
Traditionally, development and operations teams have been at a crossroads because their goals compete: operations wants to ensure stability, which means less change, while developers want to roll out new or upgraded applications with more features. While stability and availability of critical applications must be virtually at 100 percent, new features and functionality also need to be churned out more quickly. This convergence has led to the DevOps movement, which drives development and operations teams to work closely together. This is a good start, but the improved collaboration should not end here, however, as security must fit in to this mix.
 Security has historically been viewed by development and operations teams as a bottleneck because security by nature is about adding checks to the process of making changes and pushing out new features and capabilities. And adding security checks inherently slows things down. However, I think the majority would agree with me when I say that due to the increasing number and sophistication of cyber-attacks, security is an essential component of any successful organization. This leads to the question: how can organizations maintain and improve security while continuing to improve agility?
Security has historically been viewed by development and operations teams as a bottleneck because security by nature is about adding checks to the process of making changes and pushing out new features and capabilities. And adding security checks inherently slows things down. However, I think the majority would agree with me when I say that due to the increasing number and sophistication of cyber-attacks, security is an essential component of any successful organization. This leads to the question: how can organizations maintain and improve security while continuing to improve agility?
Blending security into the DevOps (Development and Operations) mix can enable organizations to achieve improved agility and operational excellence while improving the necessary checks and balances before changes are pushed in production. Integrating security with DevOps becomes even more important as organizations look to add next-generation infrastructure and transition from physical data centers to private/hybrid clouds. Here are three tips effectively to integrate security into DevOps:
- Collaborate – Having collaboration between these three disparate, yet connected teams is important. This becomes readily apparent when considering the process for making security changes. In order to ensure the proper checks and balances and provide visibility from all angles (i.e. application connectivity needs, broader network requirements, etc.), all of the stakeholders must understand and be involved in the change process from the beginning rather than working in silos. Improving the collaboration between the development, operations and security teams provides opportunities to explore other strategies to further improve the business as well as enable a more secure and agile network environment. By automating processes, it can help to reinforce collaboration as well as communication.
- Communicate – RebelLabs recently conducted a survey of approximately 620 enterprise engineers and the survey results revealed that traditional IT Op teams require 41 percent more time for communication and 26 percent more time for firefighting than DevOps oriented teams. Results also showed that IT Op teams spend less time on task automation and infrastructure improvements. This suggests that communication is tied tightly with collaboration or rather it is difficult to have one without the other. This is evident in the security change process, where an application owner may demand a connectivity change, network operations must process the change and security must guarantee that the change is made in a secure manner that doesn’t create any new or additional risks.
- Co-ownership – The development, operations and security teams are embedded more into the fabric of the other through the DevOps model. Code should not simply be thrown by developers over the fence to operations to push into production and the operations team should not stay away until code is ready to be implemented in a production environment. The same is true for infosecurity. In order to ensure that the application code is secure, the information security team should be involved with the developers from the beginning. Additionally, the operations team needs to ensure that the changes pushed into the network do not develop any new or additional risks. Having the responsibility shared across the development, operations and security teams helps to facilitate teamwork and improve the process around publishing new functionality. Sharing these responsibilities also helps to demonstrate compliance, security enforcement, and operational efficiency.
DevOps is all about agility, but without security tied in, operational excellence is still not fully achieved.
Looking for the best IT management solutions? Browse top product reviews and blog posts at the IT research center, or compare the industry’s top solutions by pricing and key features in our free IT management software reports.
[This article was syndicated with permission from security policy management company AlgoSec]





